The quantum threat will affect key management, PKI, TLS, database
protection, blob storage, backup security, authorization, and others.
Tip
Get aboard on the transition to postquantum cryptography now. There is progress in the development of quantum computing. Quantum computers will be able to break today’s public-key cryptography and hence compromise the security of digital communications.
CYBERCRYPT can provide organizations that develop digital products and services with post-quantum cryptography for use cases like encryption in transit and at rest as well as application-layer encryption.
Quantum threat
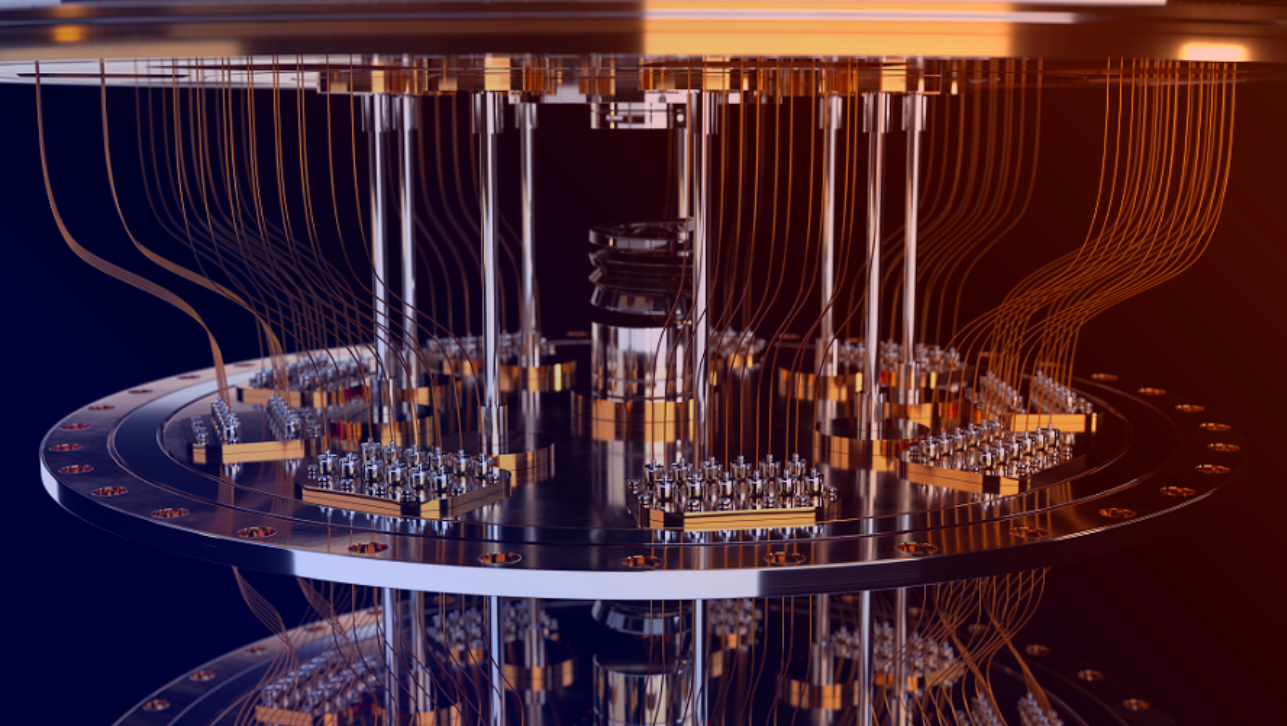
In the last decades, researchers around the world have been and are still working on the development of quantum computers. A quantum computer is an amazing technology with a computational power that makes it possible to solve yet unsolved problems. Quantum computers also come with the ability to run Shor’s algorithm which can quickly find the prime factors of a large integer or compute a discrete logarithm in large groups. This implies that today’s public-key encryption algorithms such as RSA and ECC will be vulnerable in a post- quantum world. Moreover, modern symmetric algorithms like AES and SHA will be affected, however, to a smaller extent.
Example: TLS 1.3
Today's public-key cryptographic primitives such as digital signature schemes RSA-PSS and ECDSA as well as key establishment schemes like DH and ECDH used, e.g., in TLS 1.3 will be insecure in the presence of the quantum threat.
Why is it high time to plan the transition to post-quantum cryptography?
In the presence of quantum computers, today’s public key encryption algorithms will be vulnerable. By transitioning to post-quantum cryptography, your software will be protected against quantum attacks, also in the long term.
In August 2015, the National Security Agency (NSA) announced their preliminary plans for replacing the Suite B cryptography specified by the National Institute of Standards and Technology (NIST) by post-quantum cryptography. They recommended organizations not yet using the Suite B cryptography to transition directly to post-quantum cryptography. They especially highlighted that the growing popularity of ECC did not align with the upcoming need for post-quantum cryptography as ECC is not post-quantum.
In 2016, NIST also announced the need for post-quantum public-key encryption algorithms, and shortly after they started a competition-like standardization process of post-quantum KEM’s and digital signatures. Today, the 82 initial submissions have been reduced to 7 finalists and 8 alternates. It is expected that the winners will be announced by the end of March 2022 where draft standards will then be available.
Progress in the development of quantum computers. Companies such as IBM, Google, and Microsoft are developing quantum computers, and on March 14th 2022 Microsoft’s Azure Quantum program announced that they had reached a historic milestone: After many years of research, they had finally developed so-called topological qubits. The experts from the team call the development of topological qubits a key breakthrough in science as they believe it to be the most promising path to developing a scalable quantum computer.
In a memorandum on improving cybersecurity published by the White House in January 2022, it was announced that within 180 days of the date of the memorandum, organizations in the US must identify any instances of encryption that are not post-quantum and report a timeline to transition to post-quantum encryption.
In March 2022, the Cloud Security Alliance (CSA) highlights the importance of post-quantum cryptography. On CSA’s website, they show a ”countdown clock to quantum”, a countdown to April 14, 2030, the date by which they estimate that quantum computers are ready to break today’s public-key cryptography.
CYBERCRYPT and PQC
Post-quantum cryptography (PQC) is a set of cryptographic algorithms and protocols that are resistant to quantum attacks. Digital products and services should start migrating to post-quantum cryptography now. At CYBERCRYPT, our own cryptographic technologies including CYBERCRYPT D1 are designed to be post-quantum. Reach out to us if we should provide you with post-quantum cryptography. Our team of highly qualified cryptographers will be able to assist you based on our 20+ years of experience in cryptography incl. 100 research papers published by us in this area as well as our toolbox of cryptographic technologies.